How To Change The Name On A Gpg Key
This tutorial series volition teach yous how to employ GPG (Gnu Privacy Baby-sit) in the Linux terminal, so yous volition be able to send encrypted email messages and digitally sign documents.
What is GPG?
GPG (GNU privacy guard) is an open-source implementation of the OpenPGP protocol. Information technology's a free alternative to the PGP program. So what is PGP? PGP (Pretty Expert Privacy) is an encryption program adult in 1991 by Phil Zimmermann.
PGP and GPG are unremarkably used for two things.
- Encryption: encrypt emails and files like Edward Snowden does every day, so bad actors can't read your encrypted emails and files.
- Signing: create digital signatures for signing documents. You can also use information technology to digitally sign all your outgoing emails, so the recipient can know the electronic mail hasn't been tampered with. The software repository of your Linux distribution is also signed by a PGP primal, so you can exist certain that yous are not downloading malware when running commmand
sudo apt updateorsudo dnf update.
PGP and GPG are sometimes interchangeable. You tin say you take a PGP central or a GPG cardinal.

Encryption at rest
If you lot run your ain electronic mail server, you lot should know that a TLS document tin can exist used to encrypt email traffic between SMTP servers, then why use GPG?
- A TLS certificate is used to encrypt email traffic in transit. Hackers can't snoop on your email traffic and extract valuable information.
- GPG is used to encrypt emails at rest. If someone gains access to your computer, your emails are still safe, because only y'all have the passphrase to decrypt the electronic mail letters.
Stop-to-Terminate Encryption
An email server admin can configure the server to encrypt all electronic mail messages at balance for users. This is a form of centralized encryption. Mayhap the e-mail server admin has the private cardinal and can decrypt all electronic mail messages. Y'all can't be certain that they can't decrypt your emails.
In dissimilarity, GPG uses cease-to-stop encryption, meaning the encryption is done on the user'due south computer before sending it out to the recipient. The private key is stored on the user's computer, so the electronic mail server admin tin't decrypt the email message.
Hint: It'south non required to run your own email server. You can use GPG with Gmail, Yahoo Mail, or whatsoever e-mail account.
six Parts Tutorial Series
The tutorial serial is divided into six parts:
- Part 1: Generate Your Public/Private Keypair
- Role 2: Public Fundamental Management
- Part iii: Encrypt and Decrypt Message
- Part 4: How to encrypt and decrypt emails in the Thunderbird e-mail customer
- Part 5: Digital Signature
- Part 6: How to Verify PGP Signature of Downloaded Software on Linux
This is part 1 of this serial. At the end of this commodity, you should be able to generate your ain public/private key pair and a revocation certificate, which is used to revoke your public/private key pair when your private central is compromised or yous forget the passphrase for your private fundamental.
Step 1: Install GPG
GPG is pre-installed on most Linux distributions, though you can run the following commands to install information technology.
- Debian/Ubuntu:
sudo apt install gpg - Fedora/CentOS/RHEL/Rocky Linux:
sudo dnf install gpg - Arch Linux:
sudo pacman -S gpg - OpenSUSE:
sudo zypper install gpg
This commodity uses the modern GPG 2.2 / 2.three version. The legacy version (i.x) won't be discussed. Most Linux distributions come up with the modern ii.2 / 2.3 version.
- macOS users tin can use the gpgtools to install GPG.
- Windows users can install the GPG4win packet. (You really shouldn't be using Windows if you care about privacy.)
Step 2: Check Your GPG Version
Let'south check the GPG version on the arrangement and some interesting tidbits. Run the following command.
gpg --version
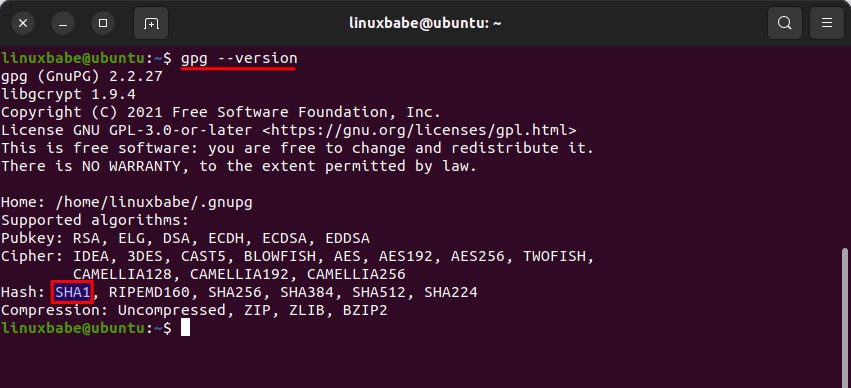
As you can see, I'm using GPG 2.2.27. We too know that the configuration directory is ~/.gnupg, which will hold our public/private primal files. It too tells u.s. what algorithms are supported.
If you expect closely, you can come across that the insecure hash algorithm SHA1 is still supported in version 2.2.27 SHA1 is obsolete and you don't want to apply it to generate digital signatures.
Pace three: Create Your Public/Private Fundamental Pair and Revocation Document
Run the following command to generate your central pair. GPG defaults to RSA keys. We use the --expert manner because information technology allows us to create more than secure keys (ed25519).
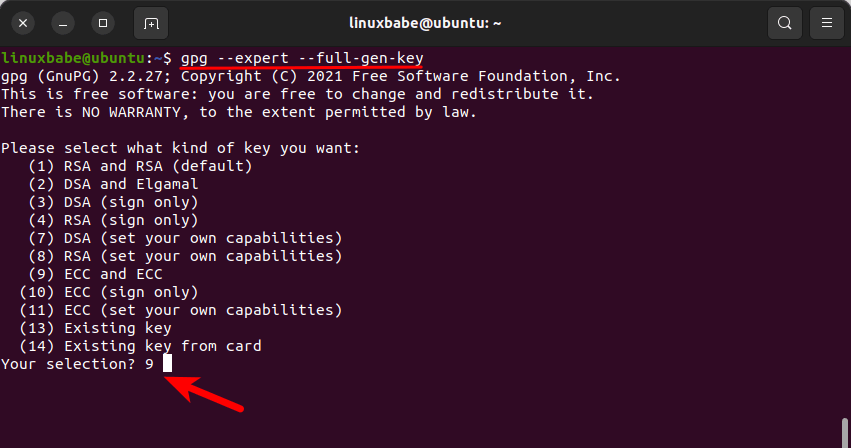
gpg --skillful --full-gen-key
Hint: If yous generate GPG cardinal on the console or in a pure command-line environment, you should run this command instead: gpg --practiced --pinentry-mode=loopback --full-gen-cardinal.
It asks you what kind of central you want. there're 14 options. Choose the 9th option, so it will create an ECC (Elliptic curve cryptography) public/individual keypair and an ECC signing key.
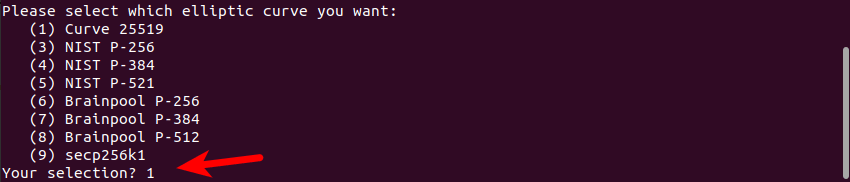
Then it asks yous which elliptic curve you desire. Choose the starting time selection to create ed25519 keys.
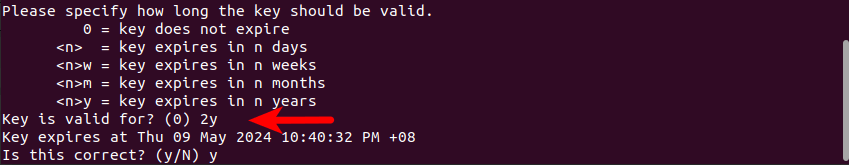
Adjacent, cull how long the key should be valid. ii years is fine. You can ever extend the fourth dimension when it's most to expire. Then it asks you if it's correct. Detect that the default is No, press y then Enter to confirm it's correct.
Now we need to provide some user identification data for the key. This is important considering this information will be included in our key. It'southward ane way of indicating who is the possessor of this key. The email accost is a unique identifier for a person. You can get out the Comments field blank. Really, you should never enter annihilation in the Comment field.
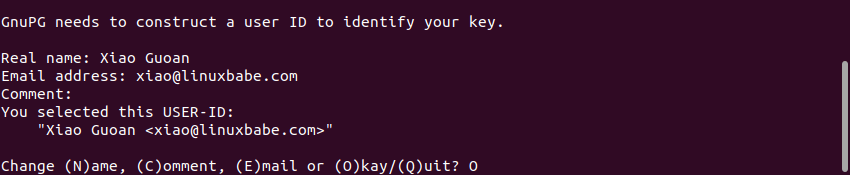
Afterward that, it asks you lot to enter a passphrase to protect your individual key. Enter a good and long passphrase and call back it. If you forget this passphrase, you won't be able to unlock your private key.
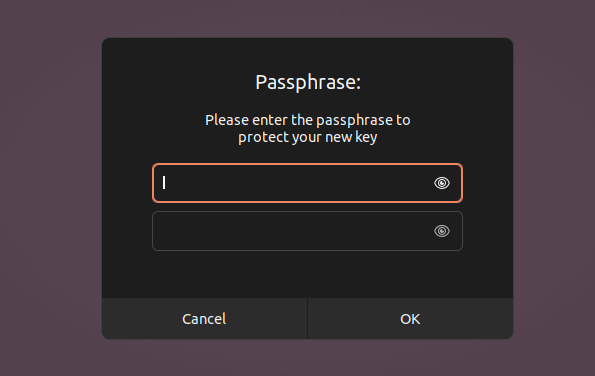
Once you enter and confirm your passphrase. GPG will generate your keys in a jiffy.
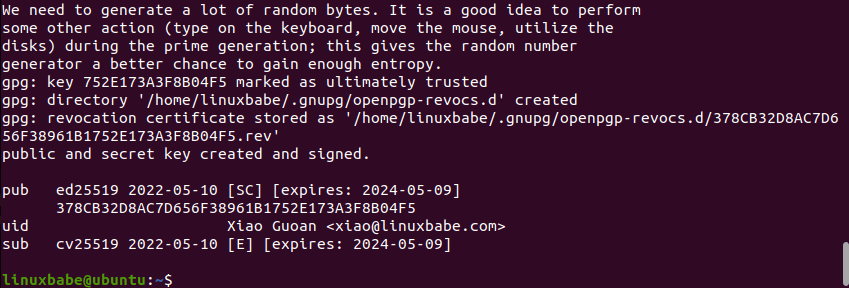
Nosotros can see from the above screenshot that GPG created a unique identifier for the public key (752E173A3F8B04F5). This unique identifier is in hex format. When someone wants to download your public key, they tin can use your email address or this hex value as a unique identifier.
GPG also created a revocation certificate.
Your private key is stored under the ~/.gnupg/private-keys-v1.d/ directory. There are 2 files with the .key extension. You should never share your private key with anyone.If your individual key is compromised, you can use the revocation certificate to revoke your public key, which ways you tell the rest of the earth that this public key shall not be used anymore.I suggest that you lot open this revocation certificate with your text editor to run across what's inside there.
The public primal ID (752E173A3F8B04F5) matches the last 16 bits of the fundamental fingerprint. The key fingerprint is a hash of your public central.
Step 4: Consign Your Public Central
Other people need your public key to send an encrypted message to you and only your private key can decrypt information technology. Use the following control to export your public cardinal. The --armor option means that the output is ASCII armored. The default is to create the binary OpenPGP format.user-id is your email address.
gpg --armor --consign user-id > pubkey.asc The exported public key is written to pubkey.asc file. Give this file to anyone who wants to send an encrypted message to you.
Step 5: Consign Your Private Central
Consequence the following command to consign your private key.
gpg --export-hush-hush-keys --armor user-id > privkey.asc The exported fundamental is written to privkey.asc file.
Step six: Protect Your Private Key and Revocation Document
Your private key should be kept in a safe identify, similar an encrypted flash drive. Care for it like your house key. Never share it with others. And yous must remember your passphrase, otherwise, you tin can't unlock your private central.
You lot should also protect your revocation certificate. If others have your revocation certificate, they can immediately revoke your public/individual key pair and generate a fake public/private key pair.
Next Step
In part 2 you volition learn how to upload your public key to a primal server, then others can import your public key and ship yous encrypted messages. Accept care!
- A Practical Guide to GPG Part 2: Public Key Direction
Source: https://www.linuxbabe.com/security/a-practical-guide-to-gpg-part-1-generate-your-keypair
Posted by: thorntonxvier1937.blogspot.com

0 Response to "How To Change The Name On A Gpg Key"
Post a Comment